Building a Secure Crypto Wallet App: Architecture, Security, and Real-World Challenges
Learn how to build a secure crypto wallet—from choosing the right architecture to handling keys, transactions, and real-world edge cases across blockchain networks.
Most teams don’t start with the idea of building a wallet. They arrive there because their product suddenly needs one. A trading platform launches, a DeFi feature goes live, or a payment flow gets added — and now users need a place to hold assets. That’s usually when wallet development becomes part of broader blockchain product work, where multiple components have to interact reliably.
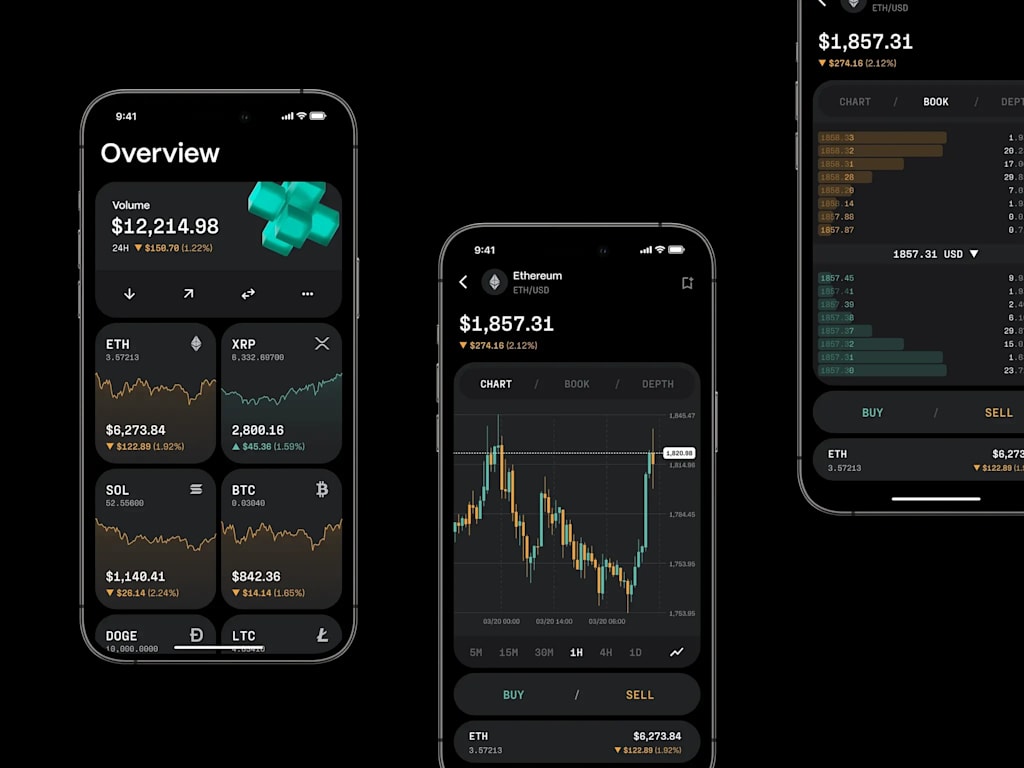
At first glance, a wallet looks simple. A balance screen, a send button, maybe a transaction history. Underneath, it’s one of the most sensitive parts of any crypto product.
What a Crypto Wallet Actually Does
A wallet doesn’t store cryptocurrency. Assets remain on the blockchain. What the wallet controls is the private key — the only proof that funds belong to a user.
That single detail defines the architecture.
When someone sends funds, the wallet builds a transaction, signs it with the private key, and sends it to the network. Signing is the critical moment. If the key leaks or becomes accessible to the wrong party, the system fails instantly.
Most early design decisions come down to two questions:
Who holds the key?
Where is the key stored?
Custodial wallets place keys on backend infrastructure. This simplifies recovery but requires strict access control and hardened environments.
Non-custodial wallets keep keys on the user’s device. That removes central responsibility but introduces risks around device security and recovery phrases.
Neither model is safer by default. Each shifts risk to a different place.
Multi-Chain Support Changes Everything
Supporting multiple blockchains is rarely just an extra feature — it reshapes the system.
Different chains behave differently. Bitcoin uses a UTXO model. Ethereum uses accounts. Transaction formats, fee logic, and signing rules vary across networks.
Every additional chain introduces new logic paths. Over time, the architecture becomes less about a single wallet and more about coordinating multiple blockchain-specific implementations under one interface.
That’s why many teams begin with a limited set of supported networks and expand carefully rather than trying to support everything from the start.
Security Is the Core of Wallet Design
Most wallet security work revolves around private key handling.
Keys are typically encrypted at rest and decrypted only during signing. The goal is simple: minimize the time a readable key exists in memory.
Recovery phrases add flexibility but also introduce risk. Anyone who gains access to that phrase controls the wallet. For that reason, many systems invest heavily in secure backup and recovery flows.
In custodial systems, security shifts to infrastructure. Hardware-backed storage is often used so keys never leave controlled environments. Signing happens internally, without exposing raw key data.
Real-world attacks rarely target encryption directly. Instead, they exploit user behavior — phishing interfaces, fake prompts, or manipulated transaction details.
Effective wallet design assumes those risks exist and reduces opportunities for error wherever possible.
Managing Transactions Reliably
Sending a transaction involves more than filling in an address and amount.
The wallet has to assemble the transaction correctly, sign it, submit it, and track its status until confirmation. During that process, multiple external factors can interfere — network congestion, delayed blocks, or incorrect fee estimation.
Reliable wallets track transaction states carefully: pending, confirmed, or replaced. They also handle unusual behavior quietly, without exposing unnecessary complexity to the user.
This reliability becomes critical in payment scenarios, where confirmation timing directly affects business logic.
Why User Experience Still Matters
Wallet UX often determines whether a product feels trustworthy.
Users interact with complex blockchain systems through simple actions — send, receive, connect. If those flows are confusing or unpredictable, mistakes happen.
Good wallet design focuses on clarity. Addresses must be validated. Fees must be visible. Steps must feel consistent.
The hardest part isn’t adding features. It’s presenting complexity without overwhelming the user.
Wallets Usually Belong to Larger Systems
Most wallets are not standalone tools. They exist alongside trading engines, payment systems, or analytics platforms.
That broader context influences architecture from the beginning. A wallet built for payments behaves differently from one designed for long-term storage or trading.
Ignoring that relationship often leads to fragile systems. Designing wallets as part of larger financial workflows leads to more stable results.
Final Thoughts
Crypto wallets look straightforward from the outside, but internally they combine cryptography, distributed infrastructure, and user-facing design.
Most complexity isn’t visible in the interface. It lives in key handling, transaction logic, and integration with blockchain networks.
Building a secure wallet is less about adding features and more about managing risk — deciding where responsibility sits, how keys are protected, and how the system behaves when something goes wrong.
That’s what separates experimental wallets from products that continue working once real users and real funds are involved.




Comments
There are no comments for this story
Be the first to respond and start the conversation.