cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.
Every night before I go
Every night before I go to bed, I ask my mother to tell me the story of the red monkey. When my mother was in a good mood, she would tell me stories about red monkeys. Once upon a time, there lived a red monkey in the forest. Stories and pictures about dinosaurs. Of course, when my mother is sleepy and wants to sleep, she will tell me that the red monkey is sleeping! The green monkey is sleeping, too! Dinosaurs are sleeping, too! Pictures on the wall! Of course I know it's my mom trying to trick me. I know my mother is sleepy. But I would love to hear about the Red Monkey. Recently there are some new storybooks at home, and my father will tell me stories. Dad's stories are nice, though sometimes I don't understand them. Come to think of it, I prefer dads when it comes to storytelling!Every night before I go to bed, I ask my mother to tell me the story of the red monkey. When my mother was in a good mood, she would tell me stories about red monkeys. Once upon a time, there lived a red monkey in the forest. Stories and pictures about dinosaurs. Of course, when my mother is sleepy and wants to sleep, she will tell me that the red monkey is sleeping! The green monkey is sleeping, too! Dinosaurs are sleeping, too! Pictures on the wall! Of course I know it's my mom trying to trick me. I know my mother is sleepy. But I would love to hear about the Red Monkey. Recently there are some new storybooks at home, and my father will tell me stories. Dad's stories are nice, though sometimes I don't understand them. Come to think of it, I prefer dads when it comes to storytelling!Every night before I go to bed, I ask my mother to tell me the story of the red monkey. When my mother was in a good mood, she would tell me stories about red monkeys. Once upon a time, there lived a red monkey in the forest. Stories and pictures about dinosaurs. Of course, when my mother is sleepy and wants to sleep, she will tell me that the red monkey is sleeping! The green monkey is sleeping, too! Dinosaurs are sleeping, too! Pictures on the wall! Of course I know it's my mom trying to trick me. I know my mother is sleepy. But I would love to hear about the Red Monkey. Recently there are some new storybooks at home, and my father will tell me stories. Dad's stories are nice, though sometimes I don't understand them. Come to think of it, I prefer dads when it comes to storytelling!Every night before I go to bed, I ask my mother to tell me the story of the red monkey. When my mother was in a good mood, she would tell me stories about red monkeys. Once upon a time, there lived a red monkey in the forest. Stories and pictures about dinosaurs. Of course, when my mother is sleepy and wants to sleep, she will tell me that the red monkey is sleeping! The green monkey is sleeping, too! Dinosaurs are sleeping, too! Pictures on the wall! Of course I know it's my mom trying to trick me. I know my mother is sleepy. But I would love to hear about the Red Monkey. Recently there are some new storybooks at home, and my father will tell me stories. Dad's stories are nice, though sometimes I don't understand them. Come to think of it, I prefer dads when it comes to storytelling!
By hope wilson3 years ago in 01
What is Workforce Framework for Cybersecurity (NICE Framework)?
The “nice cybersecurity workforce framework” refers to a structured system or plan that helps organize and develop the skills and expertise of individuals working in the field of cybersecurity. Think of it like a blueprint or guide that outlines the different roles and responsibilities within cybersecurity and the knowledge and abilities needed to excel in those roles.
By Jason Davis3 years ago in 01
Creating an Effective Data Breach Response Plan: Steps for Organizations
A data breach response plan is a crucial component of any organization's cybersecurity strategy. It provides a clear roadmap for handling data breaches effectively and minimizing their impact. Here are some key steps to consider when developing a data breach response plan:
By Essert Inc3 years ago in 01
Professor's Analysis Compares Human vs. Chat GPT
The rise of artificial intelligence (AI) has sparked curiosity about its capabilities in replicating human tasks, including creative endeavors like writing. In a recent experiment, a Singaporean journalist pitted her old writings against ChatGPT, an advanced language model developed by OpenAI, to determine if a professor could distinguish between the human and AI-generated pieces. The results shed light on the strengths and limitations of AI in storytelling, showcasing the unique qualities that distinguish human writing from its artificial counterpart.
By Nadiia Diia3 years ago in 01
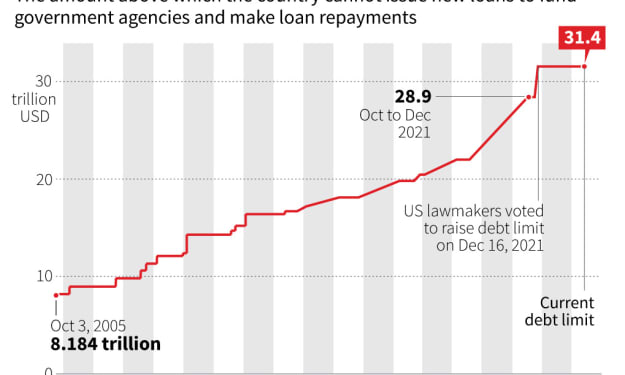
Exploring the Impact of the US Debt Ceiling Deadline on 5th June 2021 & What it Means for Businesses
The US debt ceiling deadline on June 5th, 2021, brought with it a sense of urgency and potential consequences for businesses. The debt ceiling, a limit set by Congress on the amount of debt the US government can accumulate, plays a significant role in the country's financial stability. When the debt ceiling is reached, the government must take measures to continue borrowing, or it risks defaulting on its financial obligations. This article will examine the impact of the debt ceiling deadline and what it means for businesses.
By Muhammad Uzair3 years ago in 01
(MMOBizOpps) Easy Affiliate Commissions review
Are you looking to earn easy affiliate commissions online without the hassle of product creation or technical skills? Look no further! In this comprehensive training program, we provide you with a proven formula and step-by-step instructions to help you drive sales and generate profits quickly. Whether you're a beginner or an experienced marketer, our system offers a turnkey solution with built-in offers and a done-for-you funnel, eliminating the need for hosting, customer service, or complex setups.
By outofboxreview3 years ago in 01
Why do I need web development consulting services?
Introduction In today's digital age, having a strong online presence is crucial for businesses of all sizes. A well-designed and functional website serves as a virtual storefront, allowing you to reach a wider audience and generate leads. However, navigating the complexities of web development can be challenging, especially if you lack the necessary expertise. This is where web development consulting services come into play. In this article, we will explore why you need web development consulting services and how they can benefit your business.
By cameron buttler3 years ago in 01