cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.
Office 365 Tenant-to-Tenant Migration in London: What You Need to Know
Tenant-to-tenant migrations within Office 365 are increasingly prevalent among London-based small and medium-sized businesses (SMBS), often prompted by mergers, acquisitions, or organisational restructuring. This comprehensive guide outlines the critical considerations for London SMBS embarking on an Office 365 migration, ensuring compliance, security, and operational continuity.
By Fiora Hart10 months ago in 01
Stop SQL Injection in Its Tracks: 9 Free Tools Every Ethical Hacker Should Know
If there’s one web vulnerability that refuses to die, it’s SQL injection. From small websites to enterprise platforms, SQL injection (SQLi) remains a major security concern, and for good reason. When exploited, it can grant attackers access to sensitive data, allow them to modify or delete database entries, and even take control of a server.
By Sam Bishop11 months ago in 01
Cheyanne Mallas PA: Orchestrating Cybersecurity Success Through Precision Project Management
In the digital age, data is the new gold—and like any treasure, it attracts thieves. From ransomware and phishing to insider threats and large-scale breaches, the cybersecurity landscape grows more volatile each day. Amid this chaos, one role becomes critical: the cybersecurity project manager. Leading this charge with exceptional skill and composure is Cheyanne Mallas PA, a professional known for managing high-risk cybersecurity projects with surgical precision and visionary strategy.
By Cheyanne Mallas PA11 months ago in 01
Crypto Recovery: Comprehensive Steps to Recover Lost Crypto and Safeguard Your Digital Assets with Puran Crypto Recovery
Cryptocurrency has revolutionized finance, offering a dynamic tool for diversifying investment portfolios, trading, and facilitating seamless transactions for goods and services. Its decentralized nature provides unparalleled freedom, but it also exposes users to significant risks, with $51 billion lost to crypto scams and thefts in 2024 alone. Vulnerabilities such as phishing, hacks, and human errors can lead to devastating losses, making crypto recovery a critical skill for investors. Puran Crypto Recovery (PCR), the best crypto recovery company in the USA, with a 94% success rate in 2024, stands as a trusted partner in reclaiming lost assets. This comprehensive guide outlines essential steps to recover lost crypto, protect your digital wealth, and leverage PCR’s expertise to navigate the complex blockchain landscape.
By Madelyn Bennett11 months ago in 01
Which SSL Certificate is Best for WordPress Multisite Installations?
Running a WordPress Multisite network is a smart move if you manage several sites. You get a single dashboard for updates, users, and themes, but when it comes to securing your setup with an SSL certificate, many site owners are left wondering: what kind of certificate should I use?
By Alice Martin11 months ago in 01
How to Safely Recover Stolen Cryptocurrency: A Comprehensive Guide
Realizing that your cryptocurrency has disappeared can send shivers down your spine, almost like being the unsuspecting target of a cyber heist. I understand this all too well—without falling victim myself—and that’s precisely why I immersed myself in the intricate world of crypto recovery.
By Micah Carter11 months ago in 01
Navigating the Digital Wild West: Why Cybersecurity is More Critical Than Ever
Navigating the Digital Wild West: Why Cybersecurity is More Critical Than Ever In an increasingly interconnected world, where every facet of our lives, from communication and commerce to healthcare and critical infrastructure, relies on digital networks, the importance of cybersecurity has skyrocketed. It's no longer just an IT department's concern; it's a fundamental necessity for individuals, businesses, and even nations. The digital landscape is a dynamic arena, constantly evolving with new technologies and, unfortunately, new threats.
By BELAJAR AI11 months ago in 01
Cheyanne Mallas: Project Management at the Core of Cybersecurity Innovation
Driving scalable security solutions in a rapidly evolving digital landscape In an age where data breaches make headlines and digital trust defines business longevity, cybersecurity is no longer a niche concern—it’s the backbone of organizational resilience. Behind the scenes of successful cybersecurity transformations are leaders who don’t just understand risk—they know how to manage it, structure it, and deliver outcomes through clarity and collaboration. One such leader is Cheyanne Mallas, a project manager whose impact on the cybersecurity industry continues to grow through precision, foresight, and people-first leadership.
By Cheyanne Mallas PA11 months ago in 01
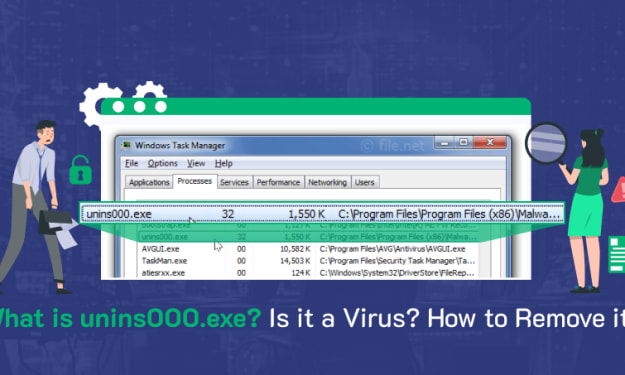
Is unins000.exe Causing Trouble? Here's What It Is and How to Get Rid of It
unins000.exe: Is It Safe or Should You Be Concerned? If you've stumbled upon a strange-looking file called "unins000.exe" on your Windows computer, you're probably wondering what it is and whether it's something to worry about. You're not alone. Many users find unfamiliar files on their systems and immediately jump to concerns about malware. It's a valid worry in today's digital world, but not everything unfamiliar is dangerous.
By Anna Shipman11 months ago in 01